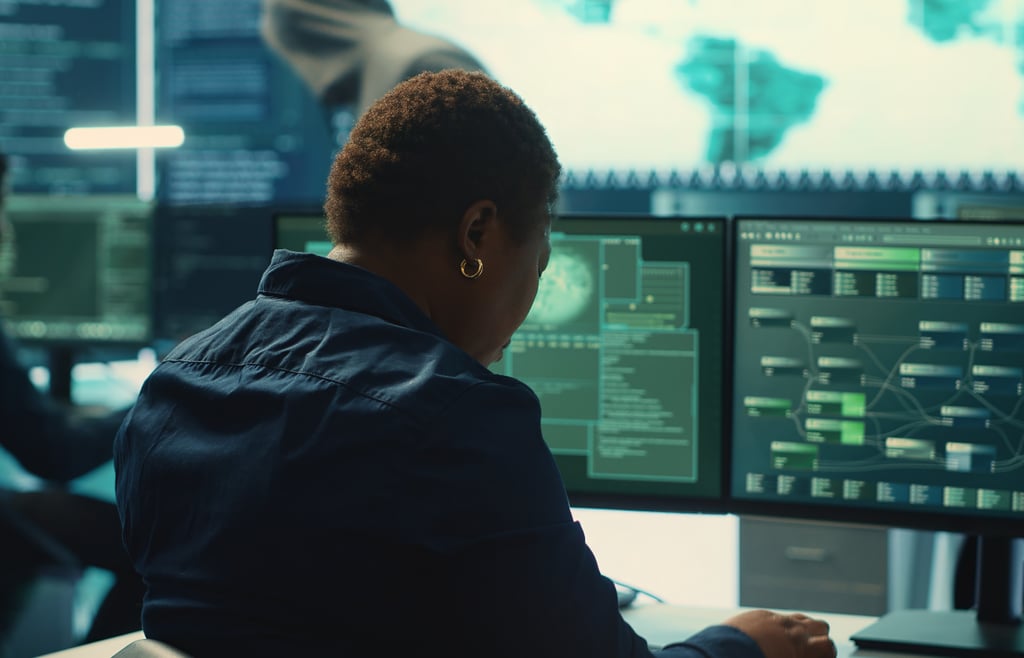
It’s dress-down Friday at Sunbelt Software’s Clearwater, Fla., headquarters. In a bland cubicle on the 12th floor, Eric Sites stares at the screen of a “dirty box,” a Microsoft Windows machine infected with the self-replicating Wootbot network worm.
Within seconds, there is a significant spike in CPU usage as the infected computer starts scanning the network, looking for vulnerable hosts.
In a cubicle across the hall, Patrick Jordan’s unpatched test machine is hit by the worm, prompting a chuckle from the veteran spyware researcher.
Almost simultaneously, the contaminated machine connects to an IRC (Internet Relay Chat) server and joins a channel to receive commands, which resemble strings of gibberish, from an unknown attacker.
“Welcome to the world of botnets,” said Sites, vice president of research and development at Sunbelt, a company that sells anti-spam and anti-spyware software.
“Basically, this machine is now owned by a criminal. It’s now sitting there in the channel, saying ‘I’m here, ready to accept commands,'” Sites explained.
A botnet is a collection of broadband-enabled PCs, hijacked during virus and worm attacks and seeded with software that connects back to a server to receive communications from a remote attacker. And these botnets are everywhere.
According to statistics released by Symantec, an average of 57,000 active bots was observed per day over the first six months of 2006.
During that period, the anti-virus vendor discovered a whopping 4.7 million distinct computers being actively used in botnets to spit out spam, launch DoS (denial of service) attacks, install malware or log keystrokes for identity theft.

Botnets filled—and easily replenished—with compromised Windows have emerged as the key hub for well-organized crime rings around the globe, using stolen bandwidth from drone zombies to make money from nefarious Internet activity, according to security experts tracking the threat.
From adware and spyware installations to spam runs and phishing attacks, CPU cycles from botnets drive a billion-dollar underground business that thrives on lax computer security and uses “money mules” to ship physical items around the world.
 Click here to read more about money mules.
Click here to read more about money mules.
Now, there is a general feeling of hopelessness among security professionals involved in finding and disabling botnets. It remains to be seen how this despair affects security products and the attitudes of the technology executives who rely on them.
“We’ve known about [the threat from] botnets for a few years, but we’re only now figuring out how they really work, and I’m afraid we might be two to three years behind in terms of response mechanisms,” said Marcus Sachs, a deputy director in the Computer Science Laboratory of SRI International, in Arlington, Va.
SRI is a nonprofit research institute that provides support for the Department of Homeland Security’s Cyber Security Research and Development Center.
The battle against the bots has been manned by volunteers who pinpoint the botnet command-and-control infrastructure and work with ISPs and law enforcement authorities to disable them. Now, there is a general feeling of hopelessness as botnet hunters discover that, after years of mitigating command and controls, the effort has largely gone to waste.
“We’ve managed to hold back the tide, but, for the most part, it’s been useless,” said Gadi Evron, a security evangelist at Beyond Security, in Netanya, Israel, and a leader in the botnet-hunting community. “When we disable a command-and-control server, the botnet is immediately re-created on another host. We’re not hurting them anymore,” Evron said in an interview with eWEEK.
“We’re fighting a war of intelligence. The botnet herders keep advancing and moving forward at a fast rate, and we just can’t keep up. There are just too many obstacles in our way,” Evron added.
The complex setup now includes the use of hijacked computers to host the DNS (Domain Name System) servers that provide domain resolution services for the rogue.
This allows a bot herder to dynamically change IP addresses without changing a DNS record or the hosting—and constant moving around—of phishing Web sites on bot computers.
Statistics from multiple sources justify Evron’s pessimism. According to data culled from Microsoft’s MSRT (Malicious Software Removal Tool), back-door Trojans and bots represent a “significant and tangible threat to Windows users.”
Since the first iteration of the MSRT in January 2005, the tool has removed at least one Trojan from about 3.5 million unique computers. Of the 5.7 million infected Windows machines, about 62 percent was found with a Trojan or bot.
Next Page: Cat-and-mouse game.
Cat-And-Mouse Game
Trend Micro, a Tokyo-based company that sells botnet mitigation technology to ISPs, estimates that more than 5 percent of all computers connected to the Internet have been used in botnets that have become more and more sophisticated over the years.
“These guys are way more advanced than you can imagine,” said Jose Nazario, a software and security engineer at Arbor Networks, in Lexington, Mass.
“We’ve seen botnets that are very carefully managed. The techniques [bot herders] use to partition the bots are very sophisticated and interesting. They’re partitioning bots on different servers based on bandwidth or location. If it’s a dial-up machine, [bot herders] know [the bot] doesn’t have much use, so they just put those in one channel and hose them with spyware and get paid for the installation,” Nazario said.
Joe Stewart, a senior security researcher at Atlanta-based SecureWorks, spends his days reverse-engineering bots and eavesdropping on botnet communications, and his findings confirm fears that bot herders are winning the cat-and-mouse game with advanced anti-detection techniques.
A classic example of the increased sophistication came with the Sinit back-door Trojan that employed a slick peer-to-peer distribution model. “With Sinit, there was no central server that could be shut down.
Each infected [machine] becomes part of a peer-to-peer network through which additional Trojans are spread to all hosts,” Stewart said.
“The bot herder would inject a command into one node and then spread it to all nodes. The thing that made it really sophisticated was the way all the commands and code were digitally signed. It was near impossible to crack,” Stewart said.
Evron, who has been tracking botnets since 1996, says bot herders are using free dynamic DNS services to quickly move machines around to avoid detection. He also has seen evidence of botnets operating like offline terrorist cells, where botnets control each other in a treelike structure.
“They’ve advanced to the point where there is no command and control to find and take down. For a while, the command and control was the weak link. Today, there’s enough redundancy and alternative control channels to keep them alive,” Evron said.
SecureWorks’ Stewart agrees that chasing down command and controls has become a futile exercise. “We’re up against guys who are in this for the long haul. This is big business for them, and we are seeing all kinds of crazy evasion tactics to stay ahead of us,” Stewart said.
Next Page: The profit motive.
The Profit Motive
The Mocbot worm attack in September provides the clearest evidence yet of the money that can be made from well-stocked botnets.
During the attack, which exploited a Windows Server Service vulnerability, security researchers at the German Honey-net Project discovered that hijacked PCs were being used to install ad-serving software from DollarRevenue, a company that pays between a penny and 30 cents per installation.
Within 24 hours, the IRC-controlled botnet seized control of more than 7,700 machines. During a four-day stretch, the researchers counted about 9,700 infections from a single command-and-control center and calculated that the attacker earned about $430 in commissions from DollarRevenue alone.
According to Stewart, the majority of botnet activity is linked to spam runs and ID theft phishing attacks.
The typical bot gets installed in thousands of machines and starts harvesting e-mail addresses stored on hard drives. It then installs and opens a generic SOCKS proxy to send massive amounts of spam.
In most cases, the bot herders rent the botnets to spammers, but Stewart and others have seen evidence of crime rings operating for-profit botnets.
These can be used for extortion (DDoS, or distributed DoS, attacks), traffic sniffing to steal clear-text data passing through a hijacked machine, keystroke logging to steal banking credentials, fraudulent clicks on contextual ad networks, and even the manipulation of online polls and games.
Randal Vaughn, professor of computer information systems at Baylor University’s Hankamer School of Business, in Waco, Texas, remains optimistic, despite a laundry list of weak links that include nontechnical computer users, law enforcement and botnet mitigation technologies.
“When you have an international problem, law enforcement organizations can’t cope. They simply don’t have the resources to deal with the magnitude of the botnet problem. They’re very involved, and they do take it seriously, but it’s very difficult for someone in the United States to coordinate with a law enforcement agency in Russia or China. I don’t think we’ll ever achieve mitigation in certain geographic areas,” Vaughn said in an interview.
Another big spoke in the wheel is the approach of smaller ISPs to deal with customers’ infected machines. “There’s no economic incentive for an ISP to sit on the phone for an hour and a half to help a customer get [his or her machine] disinfected. The cost of that is more than the subscription cost,” said Stewart. That fact, coupled with the large percentage of computer users running Windows versions without up-to-date patches, creates an environment that’s ripe for abuse.
“We need to give ISPs better tools to deal with the problem. It’s just not economically feasible to do manual remediation with customers,” Stewart said. Stewart plans to propose a community effort to create a free tool to help automate the removal of bots from an ISP’s network.
Several security vendors have started shipping anti-botnet products. In September, Trend Micro released InterCloud Security Service, a new service that provides botnet mitigation technology to ISPs, universities and other large network providers. InterCloud is capable of identifying zombie drones on a network and provides an automated remediation solution to stop them in real time.
Damballa, a stealth-mode startup with links to the College of Computing at the Georgia Institute of Technology, has raised venture capital funding to create technology that promises to pinpoint Internet traffic generated by zombie drones.
But, for now, the drones are winning.
 Check out eWEEK.com’s for the latest security news, reviews and analysis. And for insights on security coverage around the Web, take a look at eWEEK.com Security Center Editor Larry Seltzer’s Weblog.
Check out eWEEK.com’s for the latest security news, reviews and analysis. And for insights on security coverage around the Web, take a look at eWEEK.com Security Center Editor Larry Seltzer’s Weblog.











 AI 50 ListChannel Insider's editorial team spotlights the top AI leaders from MSPs, vendors, and channel businesses delivering measurable outcomes.Link to CML 100 Honorees
AI 50 ListChannel Insider's editorial team spotlights the top AI leaders from MSPs, vendors, and channel businesses delivering measurable outcomes.Link to CML 100 Honorees CML 100 HonoreesCheck out our CML 100 List to discover the top channel marketing individuals who are transforming channel marketing for their organizations.Link to HSP 250 List
CML 100 HonoreesCheck out our CML 100 List to discover the top channel marketing individuals who are transforming channel marketing for their organizations.Link to HSP 250 List HSP 250 ListView our HSP250 list to see the top Hybrid Solution Providers that have proactively embraced the future of tech.Link to The 2024 Channel Insider VIP List
HSP 250 ListView our HSP250 list to see the top Hybrid Solution Providers that have proactively embraced the future of tech.Link to The 2024 Channel Insider VIP List The 2024 Channel Insider VIP ListChannel Insider sought nominations from IT vendors, solution providers, and partners to highlight impactful collaborations. Check out our top choices here.
The 2024 Channel Insider VIP ListChannel Insider sought nominations from IT vendors, solution providers, and partners to highlight impactful collaborations. Check out our top choices here. Logically CEO on Cyber Risk, AI, and MSP Strategy
Logically CEO on Cyber Risk, AI, and MSP Strategy Video: SotaTek US CEO on AI Infrastructure Mistakes MSPs Must Fix
Video: SotaTek US CEO on AI Infrastructure Mistakes MSPs Must Fix Video: SecurityBridge CEO on SAP Security, AI Risks & 2026 Priorities
Video: SecurityBridge CEO on SAP Security, AI Risks & 2026 Priorities Video: Why Most AI Projects Fail According to Spyglass MTG CEO
Video: Why Most AI Projects Fail According to Spyglass MTG CEO Video: Harbor IT on NENS Acquisition and Why the Generalist MSP Model Is Dying
Video: Harbor IT on NENS Acquisition and Why the Generalist MSP Model Is Dying Video: Hype, Bubble, or Breakthrough? Talking All Things AI with The Neuron
Video: Hype, Bubble, or Breakthrough? Talking All Things AI with The Neuron